Project overview
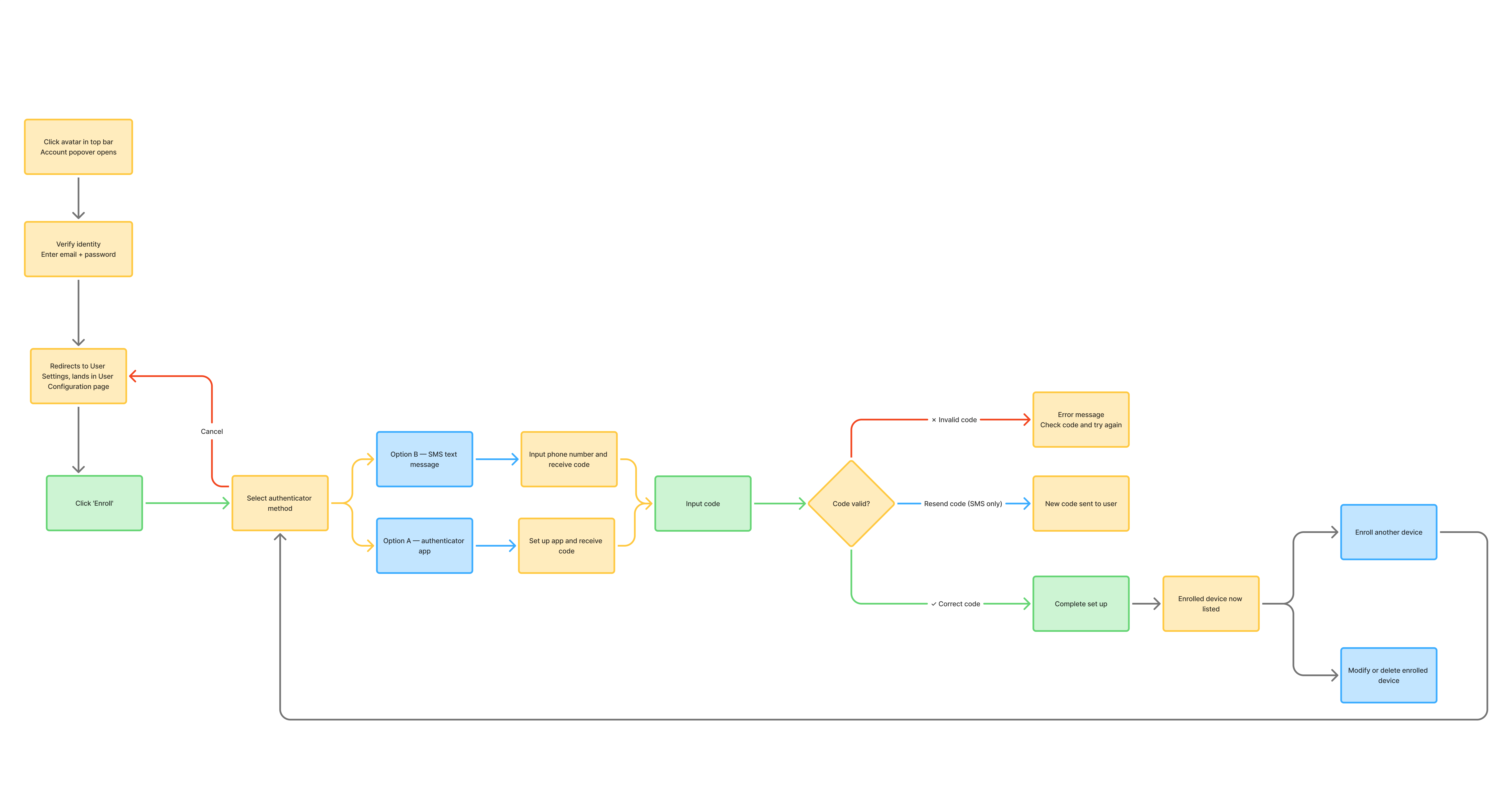
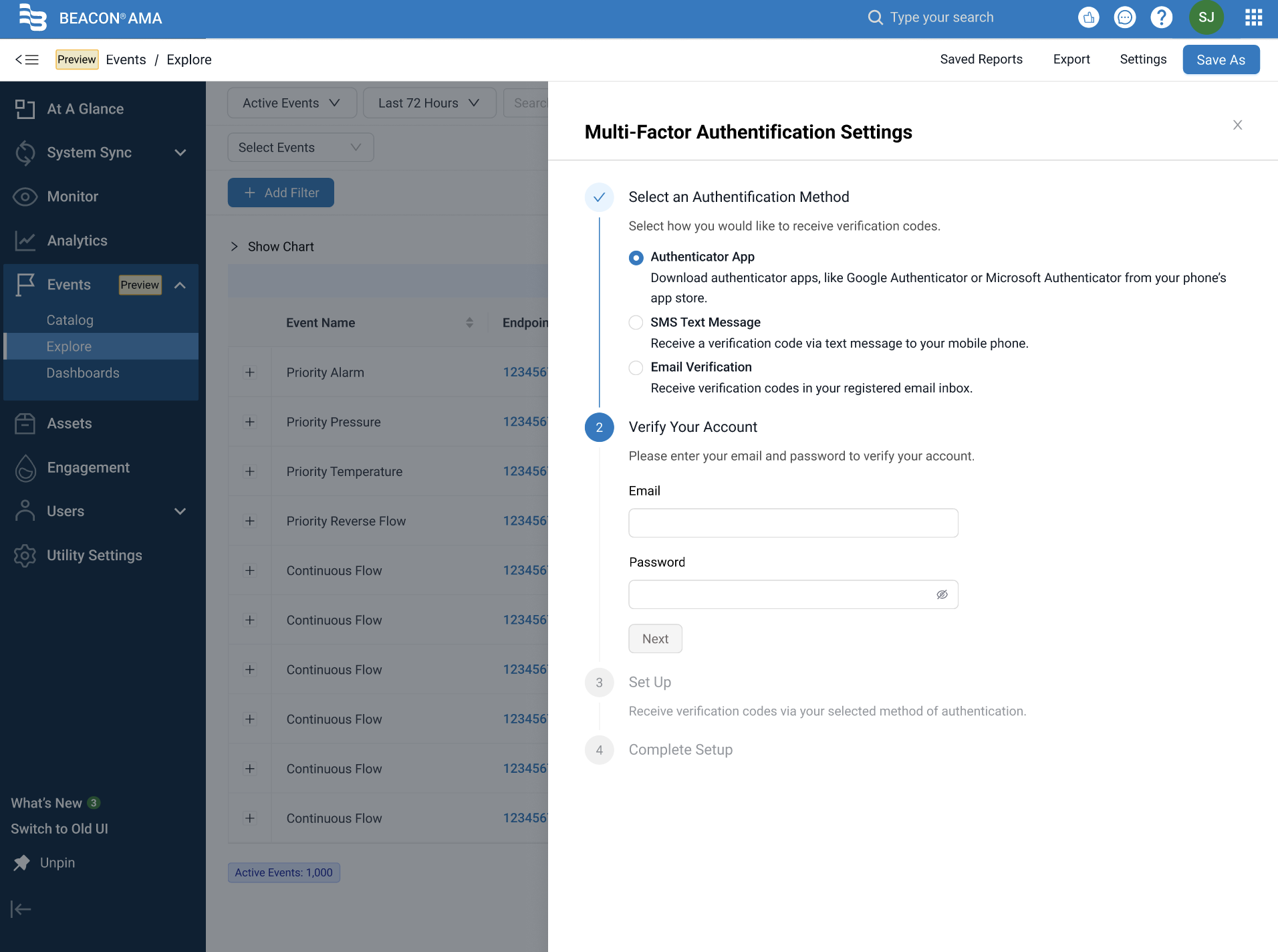
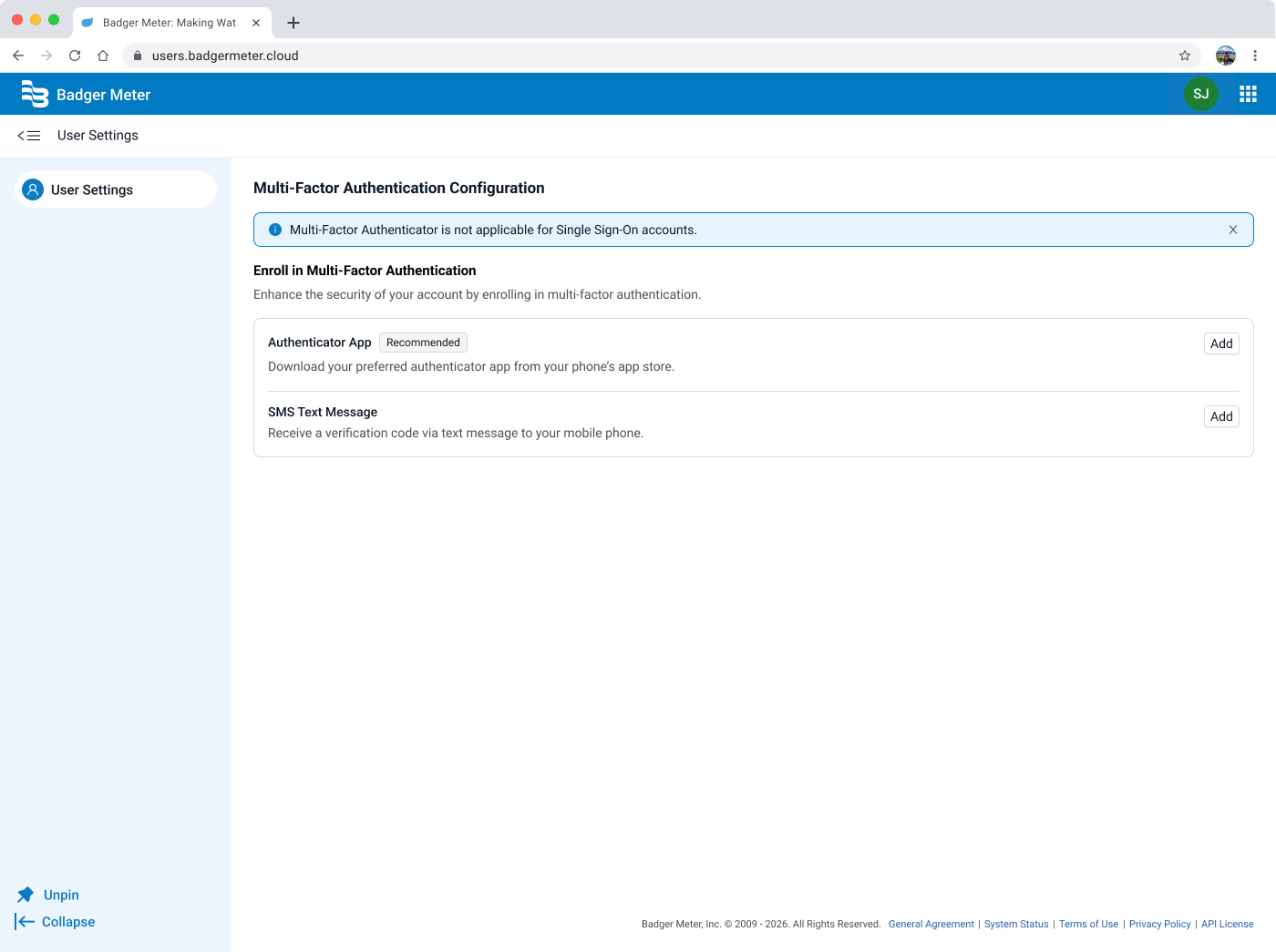
BEACON is Badger Meter's platform for utility and water management, used by utility staff members to monitor usage, manage accounts, and stay on top of data across their networks. This project introduced multi-factor authentication (MFA) enrollment to the BEACON platform for the first time.
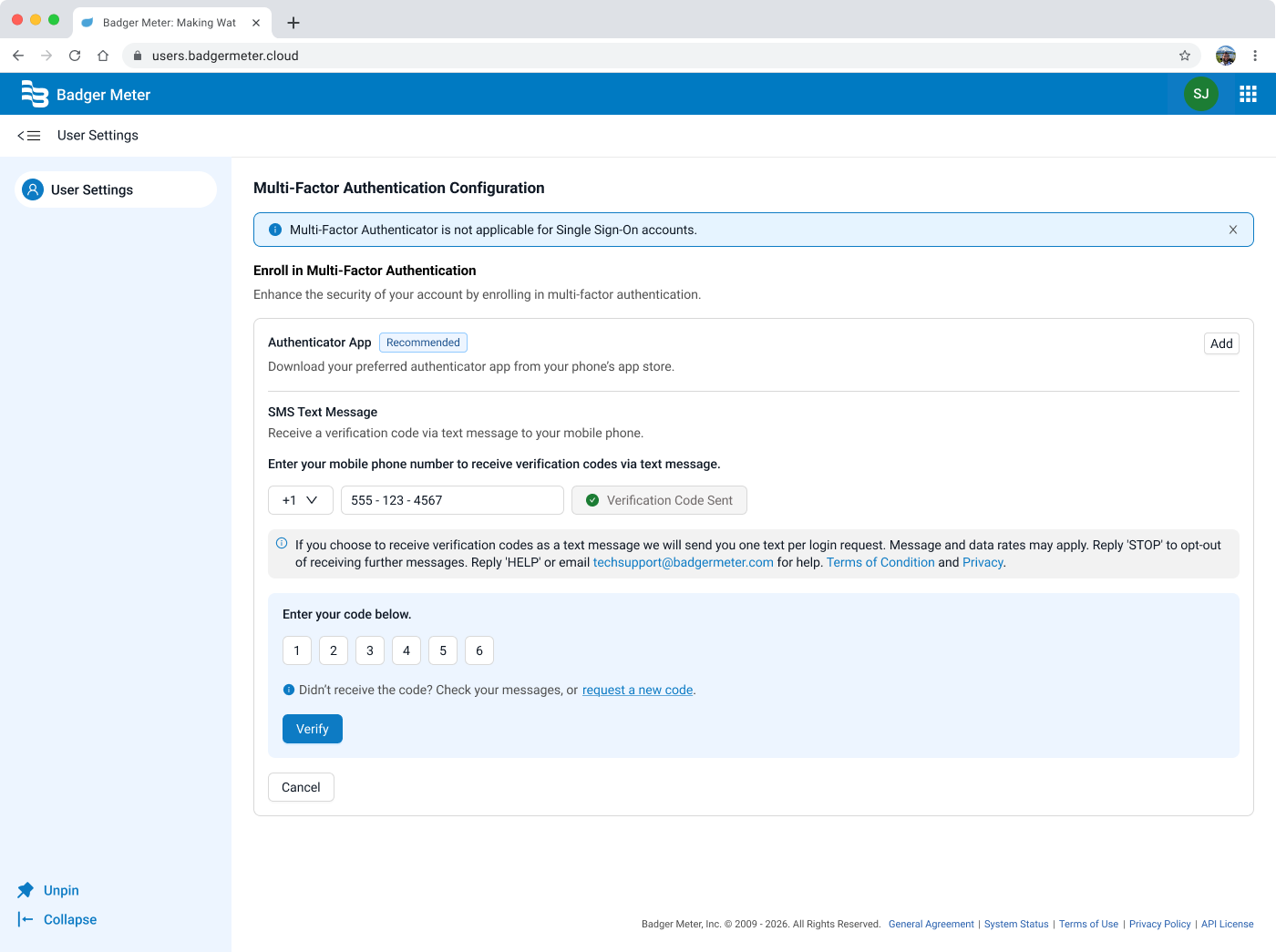
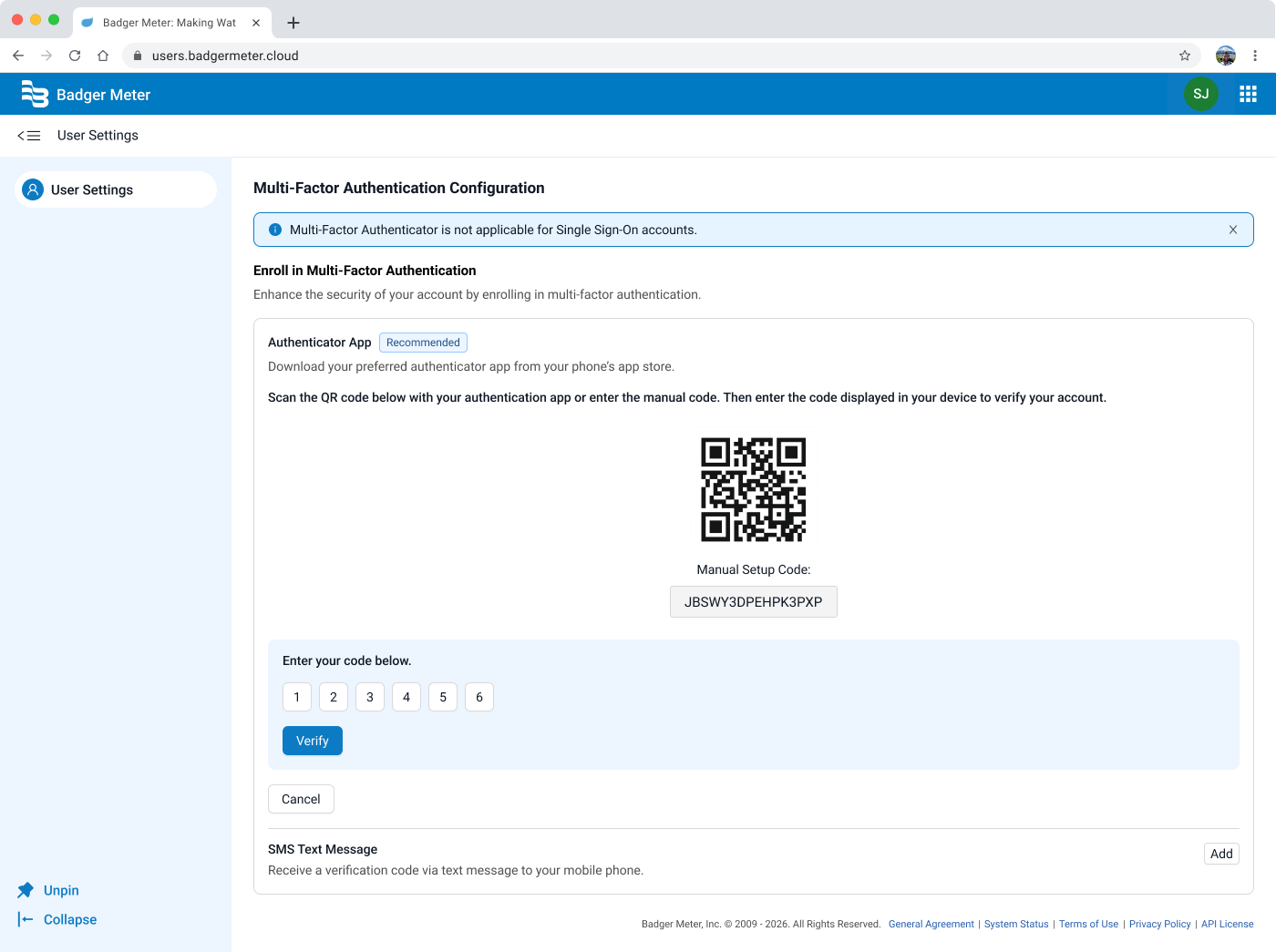
As the sole UX designer working on this feature, I was responsible for designing a self-serve enrollment experience that felt familiar, clear, and trustworthy. From the moment a user decides to set up MFA, all the way through successful verification, I had to make sure to create a seamless experience. The outcome was a dedicated security settings page, housed in a new external User Settings tab, that became the foundation for future account management capabilities.